Understanding Endpoint Security Protection
In our ever-connected digital age, have you ever wondered what keeps your devices safe from malicious attacks? Enter endpoint security protection.
-
What is an Endpoint?
Any device that connects to a network is an endpoint in the most basic sense. Consider your laptop, smartphone, or even your smart home appliances. They’re all endpoints. And each one is a potential gateway for cyber threats.
-
Why is Endpoint Security Crucial?
Imagine a vast castle. Without fortified walls, any enemy could stroll in. In our digital world, endpoints are the castle walls. Data breaches can occur without a solid endpoint security strategy, causing severe financial and reputational damage.
Components of a Robust Endpoint Security Solution
Installing an antivirus is only one aspect of it. Various technologies, like firewalls, intrusion detection systems, and anti-malware software, are included in today’s solutions.
-
Diving Deeper: How Endpoint Security Works
Ever wondered about the nuts and bolts of it?
-
Traditional vs. Modern Endpoint Security
Traditional solutions were about putting up walls. But attackers evolved. Modern endpoint security is about being proactive, constantly monitoring, and adapting.
The Layers of Endpoint Defense
Like an onion has layers (or perhaps a delicious cake?), so does endpoint defense.
-
Entry Point Layer
This is the frontline. It involves scanning incoming data for threats and blocking suspicious activities.
-
Core System Layer
Focused on the device’s operating system. It ensures that malicious code doesn’t gain a foothold.
-
Data Layer
The final defense. Even if threats get this far, encryption ensures they can’t decipher valuable data.
Threats That Endpoint Security Defends Against
It’s a wild digital world out there. Let’s take a peek.
-
Malware and Viruses
These bad boys can infect, corrupt, or delete your data. Luckily, endpoint security is on guard.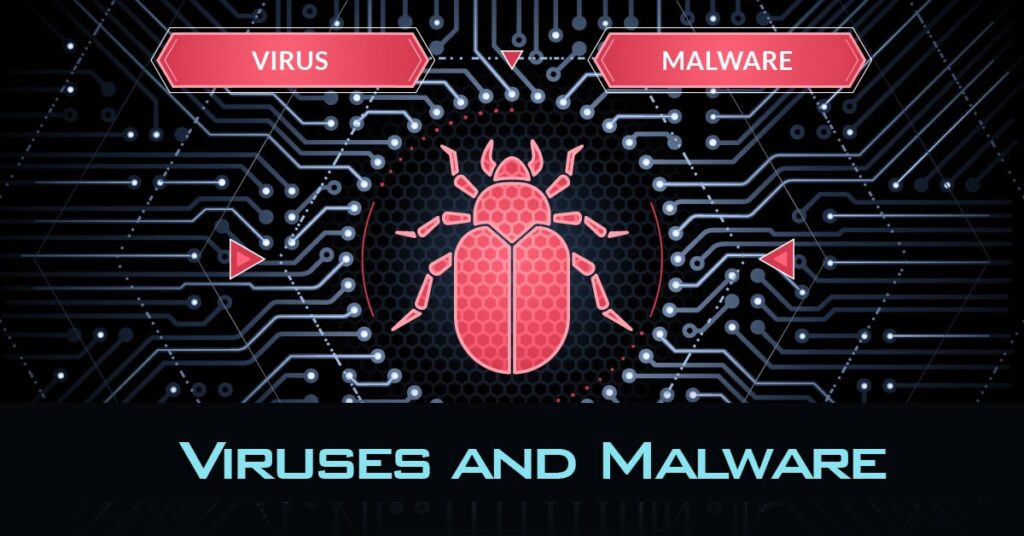
-
Phishing Attacks
Ever received a deceptive email? That’s phishing. It tricks users into giving up sensitive info. But with proper defenses, these attacks can be thwarted.
-
Zero-day Exploits
These are vulnerabilities unknown to software vendors. Sounds scary, right? Thankfully, advanced endpoint solutions can detect unusual behaviors, stopping these threats in their tracks.
-
Insider Threats
Sometimes, danger comes from within. Disgruntled employees or negligent actions can be harmful. But monitoring tools can catch unusual activities, keeping the organization safe.
Tips for Ensuring Optimal Endpoint Security Protection
Want to bolster your defenses? Here are some golden nuggets.
-
Regular Updates and Patches
It’s like getting a flu shot. Stay updated, stay protected.
-
Educating Users
Knowledge is power. Teaching users about potential threats can be your best defense.
-
Implementing Multi-factor Authentication
A double-check system ensures that even if passwords are compromised, there’s another line of defense.
Conclusion
In our modern digital era, endpoint security protection isn’t just a recommendation—it’s a necessity. With evolving threats, being proactive, adapting, and staying informed is crucial. Don’t you want to win in the cyber cat and mouse game?
FAQs for Endpoint Security Protection
Are antivirus and endpoint security the same?
No, while antivirus is a component, endpoint security encompasses a broader range of protection tools.
Why is multi-factor authentication essential?
It provides an additional layer of security, ensuring that even if one authentication method is breached, there's another barrier.
How often should endpoint security solutions be updated?
Regularly, as threats evolve, so should your defenses.
Can endpoint security protect against internal threats?
Rate our Article (How much do you like our Article